As it’s been happening from a long time for servers and clients virtualization, the Software Defined approach to networks has the goal of creating networks that are completely transparent to the underlying hardware. ZeroTier is a recent platform but still very promising to realize Software-Defined Networks (SDN) into the Cloud.
The basic idea in ZeroTier is quite simple: realizing virtual local networks with unlimited geographic extension using the Internet as a means of communication, all of that protected by ciphering and manageable from an account dashboard. The whole project is Open Source, the usage is free up to 10 clients for private networks, the upgrade is 4$/month; public networks are free and without host limits.
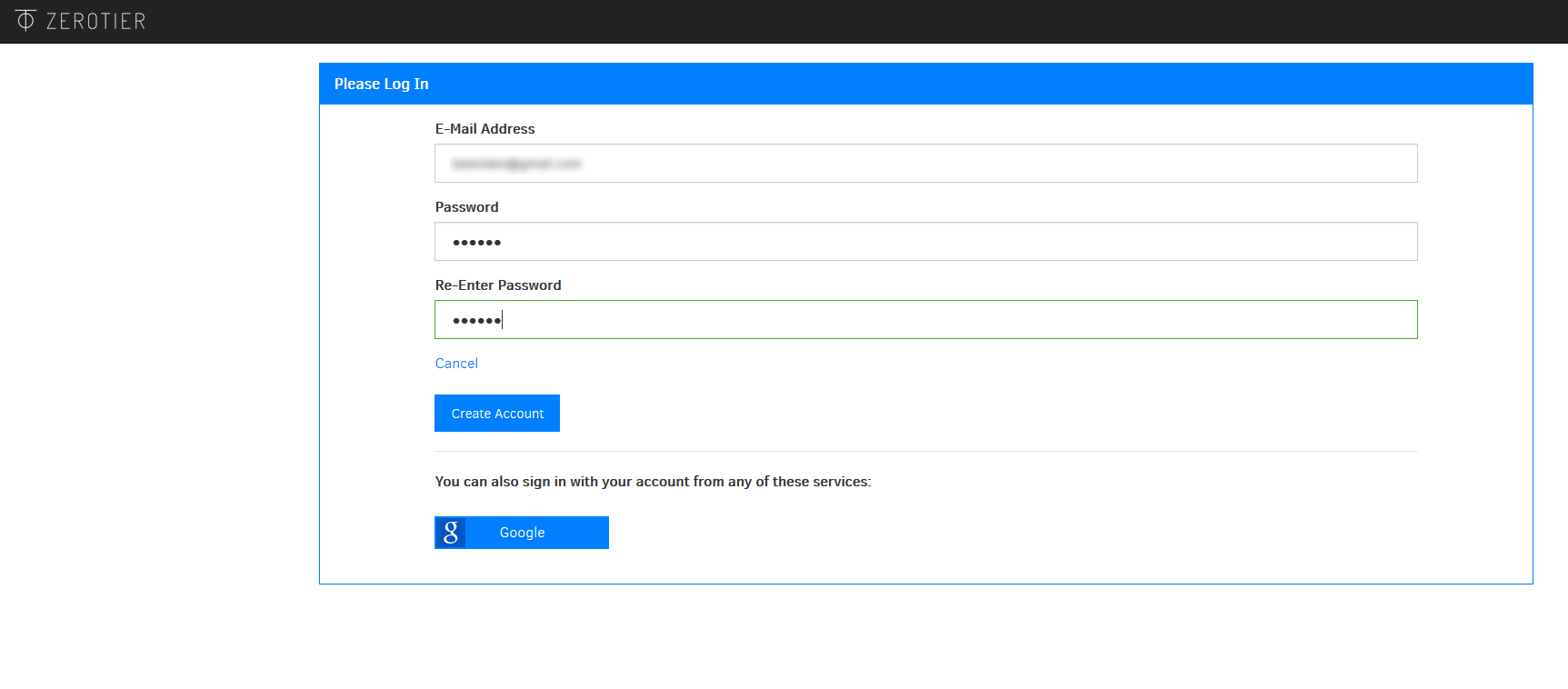
Using ZeroTier requires two steps: creating an account on zerotier.com and installing the software client.
We have tried the release 1.1.2 of ZeroTier.
Anatomy of a SDN
From a conceptual standpoint, ZeroTier creates Peer-to-Peer (P2P) networks where traffic flows amongst the participating computers, so that Root Servers (the servers used by ZeroTier as management infrastructure) have the only role of initializing connections. The main advantage is the resistance to failures: if a server becomes unreachable, the clients belonging to active networks continue to operate without downtime. Obviously it’s impossible to create new networks or disconnect from the functioning ones as long as the service hasn’t come up again. Regarding this point, the architecture of ZeroTier is quite strong, indeed it’s made of servers distributed amongst three different providers on four continents.
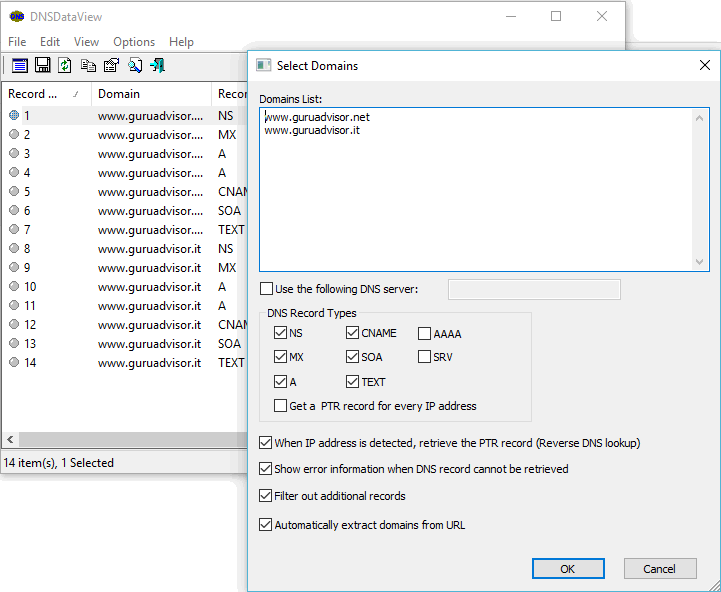
The functioning of the whole network is based on two key elements: the univocal hexadecimal ID of the device, composed by 10 characters, and the univocal hexadecimal ID of the network, composed by 16 characters. Each endpoint has a couple of public/private keys that is generated when initializing the service. The ID is calculated from the public key using a dedicate function, and the high number of possible combinations makes it hard for collisions to happen. The network ID is composed by the ID of the network primary controller (on the Root Server) which is added to the ID of the n-th network.
Networks, addresses and security
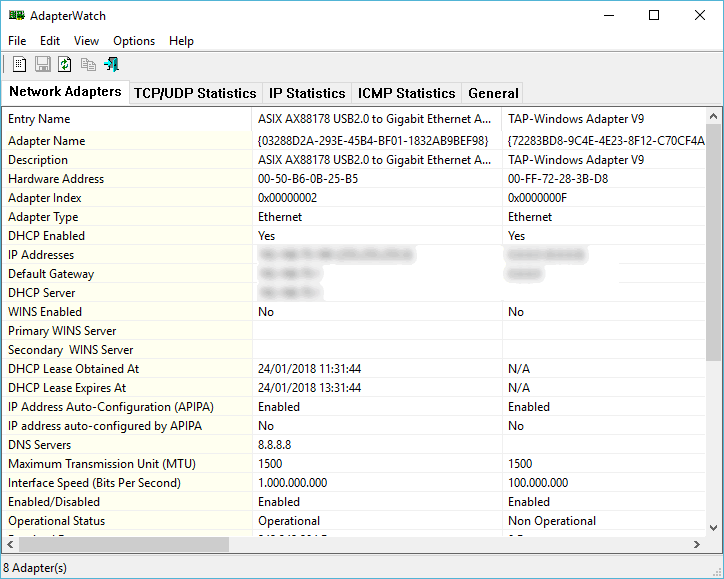
A single client can be connected to several networks, and the limit is given by the Operating System: the highest number of connections available on Mac is 32, while on Windows (XP onwards) and Linux is potentially unlimited. It’s worth to note that only the traffic with IP addresses belonging to the virtual network’s class is routed along the virtual network, whereas the remaining traffic is routed with the host’s default gateway.
A fundamental aspect when realizing a network that uses the Internet as a means of transport is the security of data: with ZeroTier all the traffic is end-to-end encrypted.
The private key is stored on the device, public keys are used to negotiate the connection and to cipher the content with a 256-bit Salsa20 stream cipher with Poly1305 authentication.
The access to private virtual LAN is guaranteed by Network IDs (which are impossible to “guess” the way they are designed) and certificates released and verified by the network controller of the same network and then shared amongst the Peers that participate to that network.
Web side management
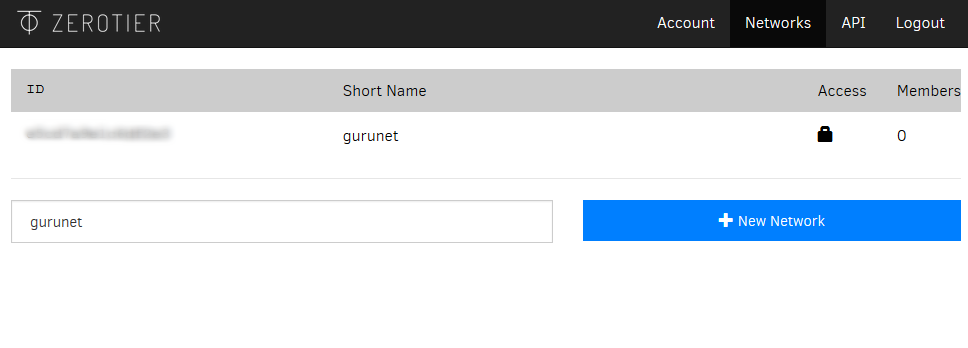
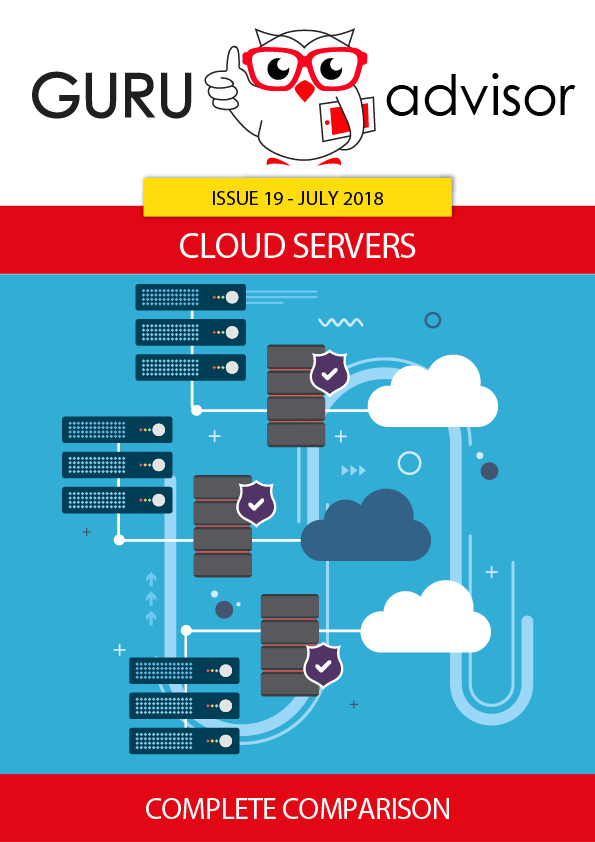
From the account dashboard it’s easy to access to the Networks menu voice from where you can manage networks; the first thing we can note is the immediate assignation of each network with an alphanumeric ID.
With the network configuration panel you can add a name and a description to the network, make it public or private, choose the type of IPs used (IPv4 or IPv6) and the limit of the enabled devices for Multicast. The IP management options are quite interesting: the suggested mode is ZeroTier managed where you can choose between 24 classes of preconfigured addresses, but you can also choose Unmanaged and then manually proceed to configure DHCP and routes.
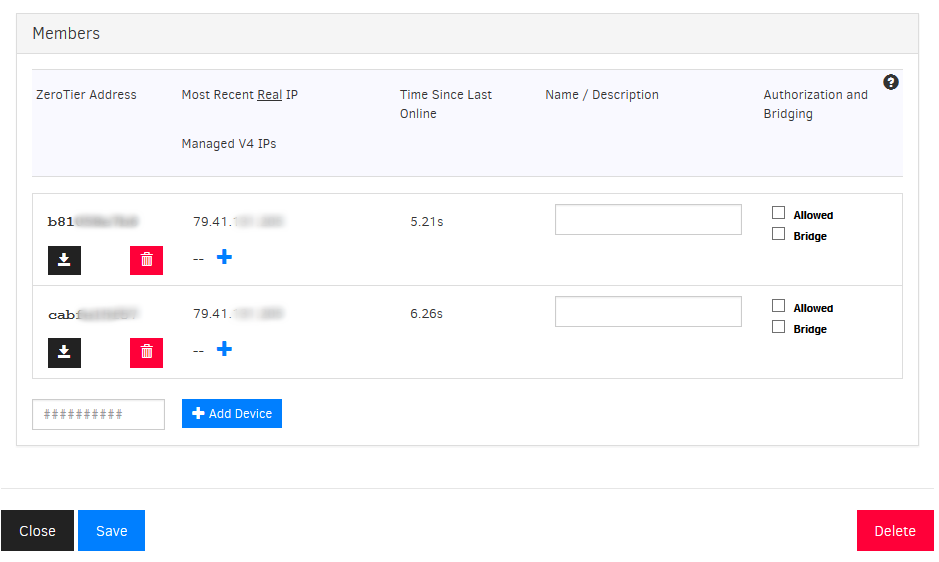
The right column is dedicated the the network’s members. You can visualize the number of connected hosts, the present configuration and add new ones or remove existing ones. The Allowed and Bridge flags are essential: the former defines if the specified client, in addition to being connected to the network, is active and reachable, while the former enables the bridged mode which let all the host traffic to flow on the ZeroTier network. The Add Device button to manually add a specific client is not missing as well.
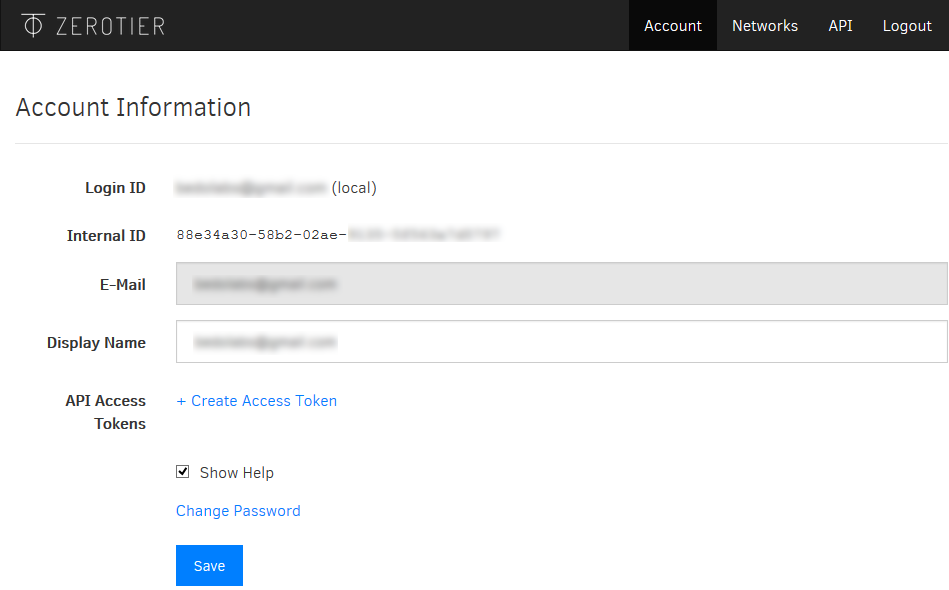
We also signal the API voice in the the menu of the personal area, from where you can consult the available APIs and read the documentation. The creation of authorized tokens is found in the starting page of the account management, where you can also insert the payment method should you need to use more than 10 hosts.
ZeroTier Client
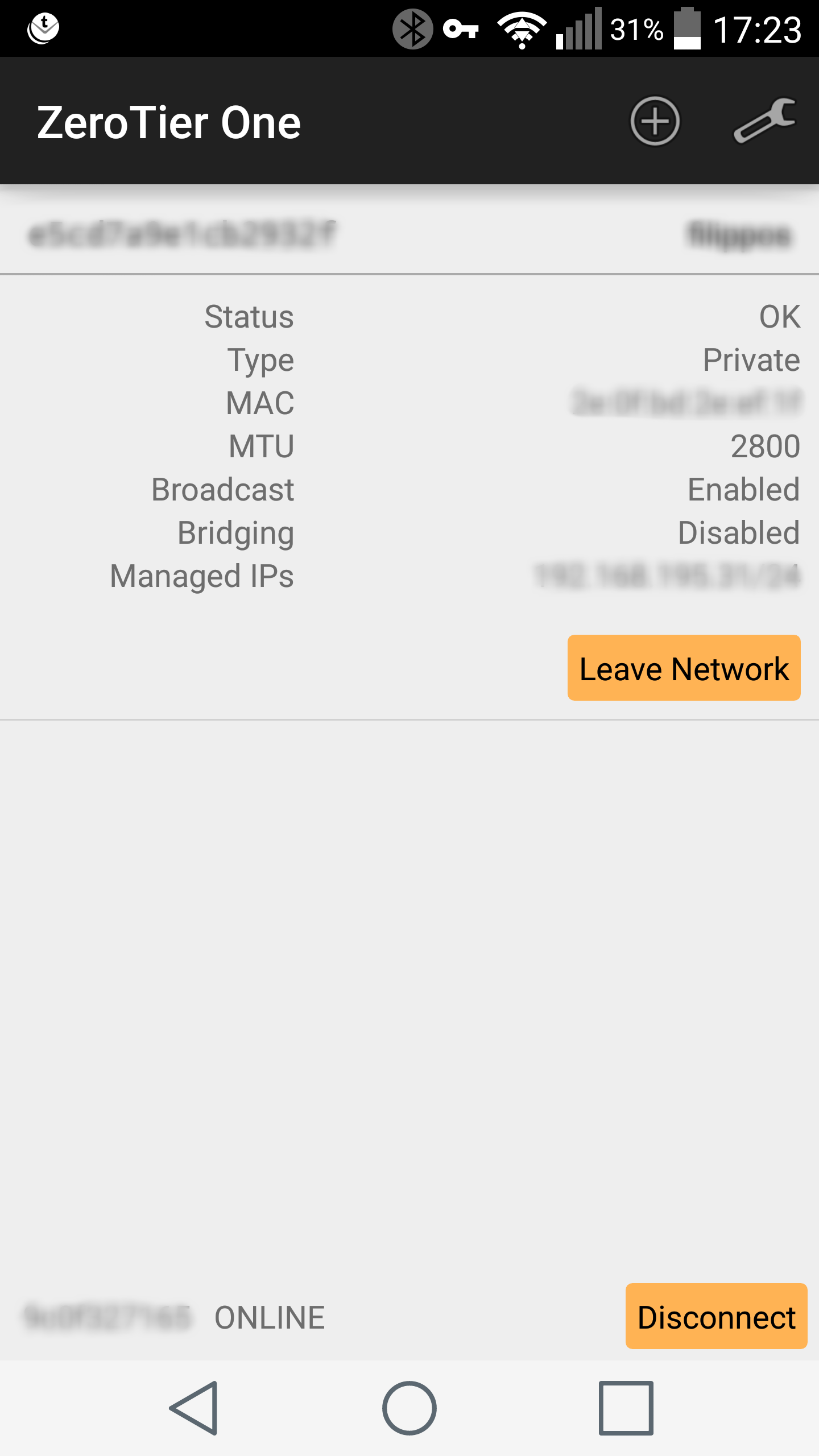
The other inlay needed to create a virtual network is the client. The client is available for free for the main desktop software (Windows, Linux and Macintosh) and hardware (Intel x86, x86_64 and ARM) platforms and also as precompiled code and source code; it can be used for ad-hoc implementations (without license for Open Source projects, with a commercial license for commercial products). There’s also an app for Android available on the Play Store that costs €5,61.
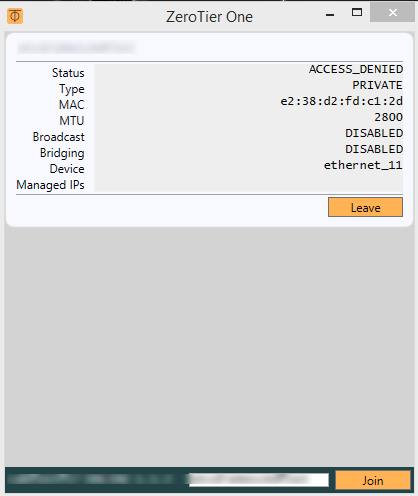
Once downloaded and installed (we have tried it on Windows 7, 8.1 and Ubuntu 14.04), a small panel pops up with, in the lower part, the network ID insertion form for the network we want to connect to. You only need to click on the Join button to connect to the virtual LAN.
As shown in the image, the panel has the fundamental information: ID and name of the network, present status of the client, IP addresses and MAC. By clicking the Leave button you can disconnect to the network.
Should the client be connected to several virtual LAN, all the relative information will appear as well.
Linux Client
The approach on Linux machines is quite alike, but naturally the command line is needed to manage the connection. Once downloaded the package for your distro (we used the 64-bit .deb package as we’re using Ubuntu), you can install it from the prompt or using the graphical package manager. In the /var/lib/zerotier-one/ a folder containing the public/private keys couple is created, and you need to make it writable by the user before launching the client.
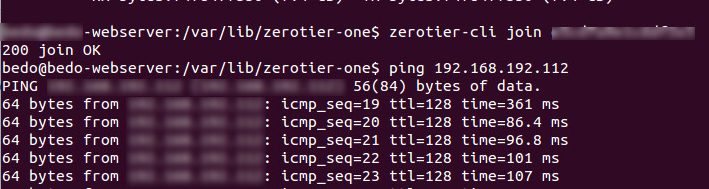
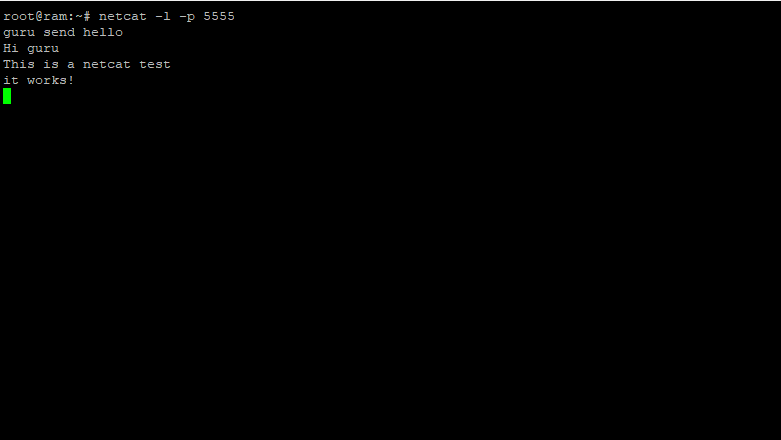
To connect to a certain network you just need this command from the CLI:
root@localhost: zerotier-cli join [network-ID]
The reply is the confirmation of the join and from this moment onwards you can ping and interact with the other machines belonging to the group.
There are some other useful commands in addition to Join to check the actual status of the networks, connected Peers and networks, etc..
Usage and impressions
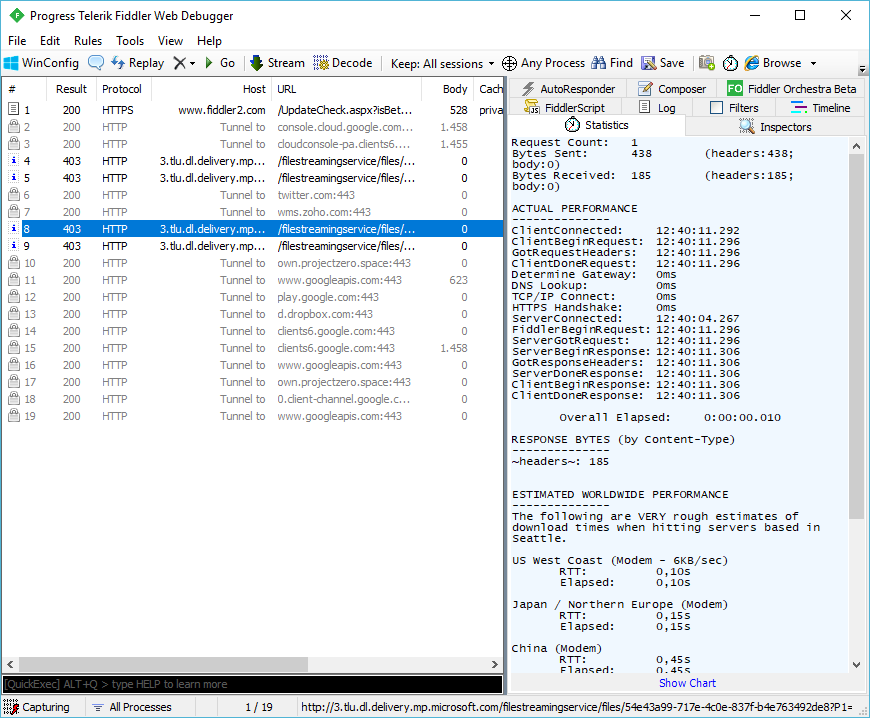
Once ZeroTier is configured and activated on all the clients, we performed some interaction tests between hosts to check the proper behaviour. First, we started some ping tests using “Managed” IPs (as how ZeroTier calls -in the dashboard- the local addresses assigned to single clients) recording reply times of 2ms for machines connected to ZeroTier on the physical LAN, and 150-200ms for clients geographically distant and on different physical networks.
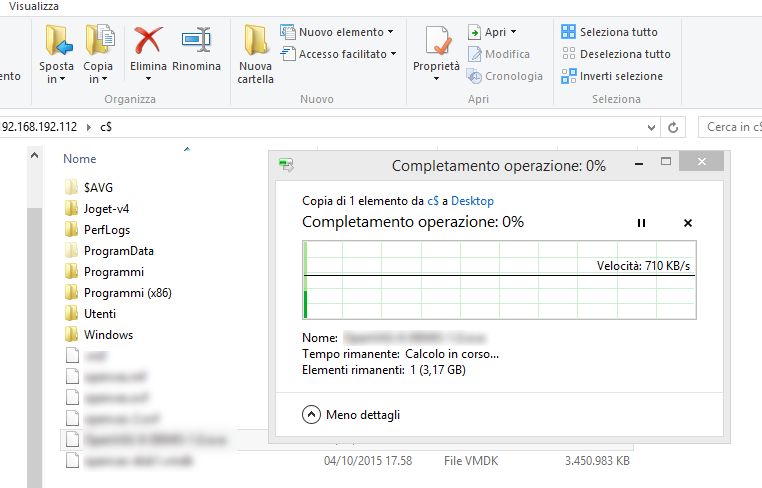
The other test was to remote desktop into Windows machines belonging to different physical LANs: in this case too we didn’t experience any connection problem and the RDP session experience is comparable to the one with, for instance, OpenVPN. As a further confirmation about the real transparency of ZeroTier with respect to the underlying physical connectivity, we tested file transfer, recording upload and download values close to the physical limit of the Internet connection used by clients.
The only problem we’ve found during our configuration and use tests is a discordance between the client configuration and the one shown in the dashboard. In some situations the client showed to be properly connected and waiting for authorization, whereas it couldn’t just be enabled in the management panel, it wasn’t even available in the member list.
The problem is resolved by manually adding the client to the dashboard by using the Add Device function.