Pritunl is an open source platform capable of realizing distributed VPN networks. By leveraging the OpenVPN protocol it allows -according to the chosen licensing model- to setup virtual network architectures. In practice, it allows to easily connect devices inside or outside the walls, also in companies with two or more branches, creating a VPN managed with advanced rules and a centralized authentication system.Pritunl integrates several services of third parties like Amazon AWS VPC (Virtual Private Cloud, it’s a virtual network space in the Cloud available to users within the AWS suite) with automated failover and Single Sign On (SSO) authentication. Integration for the use of SSO include services like Google Apps, Slack, OneLogin Okta, DUO and Radius: each one of these service can be used to guarantee users the access to the Pritunl infrastructure with their own accounts and without having to use dedicated credentials. In case the Enterprise license is chosen, which allows the installation on an unlimited number of Pritunl server, the high availability with automated failover feature can be leveraged, also given the fact that there are no master nodes, instead each node acts as the same functional level of the others. Pritunl also integrates a server replication feature, thus offering an high level of scalability for clusters. With the aim of geographically distributed installations, the platform is based on the renowned MongoDB which offers an high level of reliability (in particular as the number of nodes and users grows) associated with the chance of replication.
When realizing an extended and complex infrastructure, it’s essential to have at disposal the proper monitoring and control tools. Pritunl supports InfluxDB, a suite of tools that allow the control of hosts and clusters on the network
User experience, security and licensing
Client side, Pritunl can be used in several manners: installed on Windows, Linux, Mac or Chromebook with its software client, installed on Android or iOS with the OpenVPN client or integrated with third-party services thanks to its RESTful APIs. A fourth interesting option is to install Pritunl network devices by Ubiquiti, specifically routers of the EdgeMax family (like the EdgeRouter X we’ve tested here). The combined use of Ubiquiti hardware and Pritunl client allows the realization of VPN networks where the router is at the root of the local network, so it can directly communicate with the reference server. A plugin for EdgeMax is available at GitHub (https://github.com/pritunl/pritunl-edgemax), ready to be installed with the Web interface of EdgeOS.
When we talk about distributed networks and data traffic, security of transmitted information is always an important element to keep in mind. Pritunl server offers up to five levels of authentication, starting from the classic and not so safe numeric sequence to use as PIN, and continuing with user certificates, two-factor authentication, Single Sign On and mobile push, as in the case of using the service DUO with its smartphone app.
Pritunl offers three licensing levels with different prices: the free version allows only one installation on one server and a basic usage without any limitation on the number of users. An intermediate license called Premium is still limited to one server but offers advanced features, lastly the Enterprise version offers every feature without any limitation (failover, replication, monitoring, SSO, unlimited installation on servers, etc..). The details of the offers can be found at the documentation page of the official Website, including prices which span from 10 dollars /month for the Premium license to 50 dollars/month for the Enterprise. Pritunl also offers a paid support service with packet of 205 dollars/month or 3000 dollars/year.
Setup and use of the free version
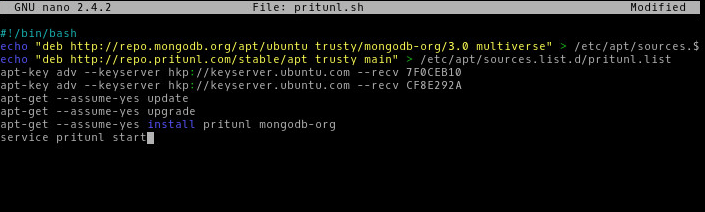
We have tried the free version of the server that, as we previously explained, allows an unlimited number of users, groups and devices per user. Such solution can be enough for small-medium companies, as in the case a company wants to offer remote access to employees in a branch office, or wants to create a network with its own clients for maintenance and remote support. The quality and detail of the documentation available on Pritunl’s Website is remarkable, several step-by-step tutorials can be found with all the needed information about basic setup (http://docs.pritunl.com). Following the dedicated guide, we have installed all components (repositories, pritunl and MongoDB) thanks to the efficient script suggested in the guide. Indeed, all you need to do is to create a file with .sh extension with the indicated commands and run it to perform a functioning installation of the VPN server.
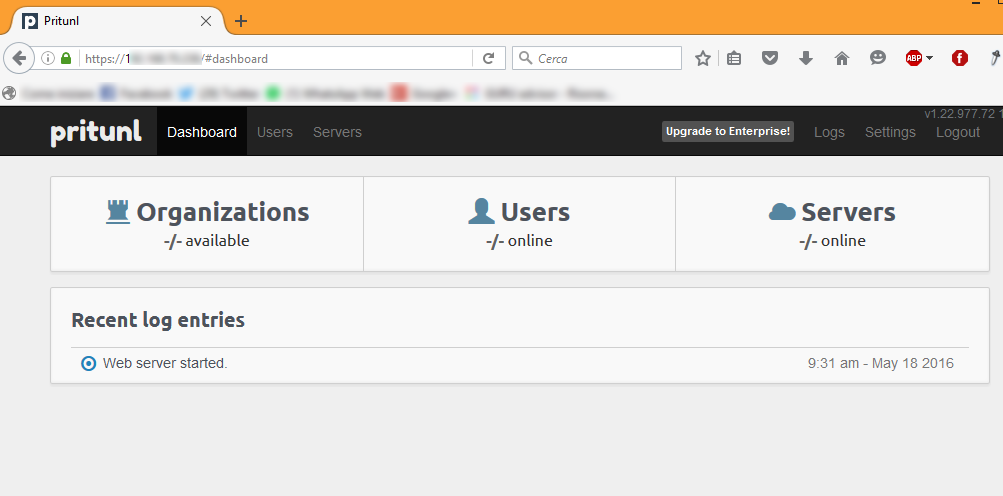
Pritunl can be managed quite entirely from the Web interface, only during the installation some specific commands require the use of the command line, for instance to secure MongoDB and increase the limit on active connections. The management panel can be reached by connecting with the https protocol the address of the server, and at the first visit the database configuration key will be asked, as well as changing the default credentials
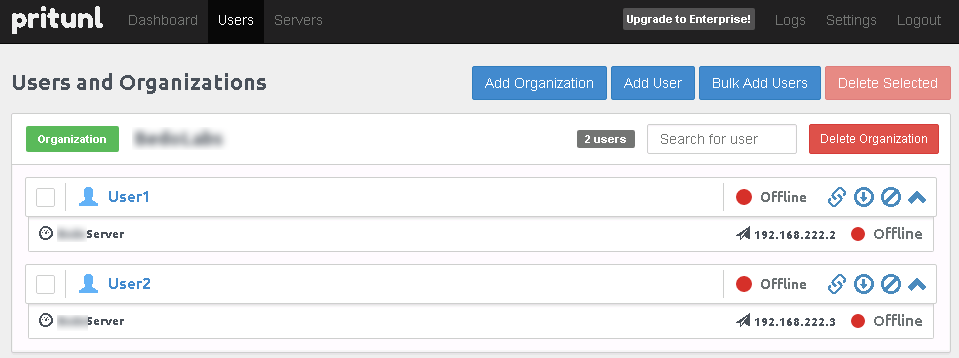
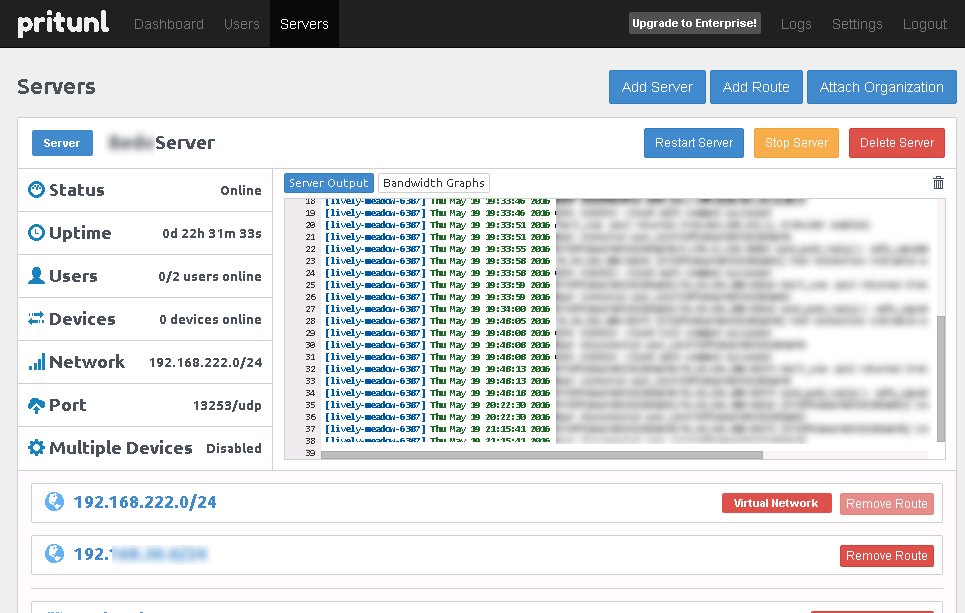
Once the initial steps are done, the interface is well organized and pleasing under a graphical aspect. The main sections of the upper menu are three: Dashboard, with a real time log of activities, Users, to create and manage both users and Organizations (an Organization is a logical subset of users) and Server, where the OpenVPN server can be managed. Analyzing more carefully the Users section we can find some features that make very easy to configure clients with the chosen user: each one can be monitored with a panel that offers information about the actual state, name of the client machine, IP address and the url to download the .tar package with the OpenVPN configuration.
The auto-download feature with a link is very handy because it just requires to copy and paste it inside the Pritunl client to obtain a complete setup and machine ready to be used. A simple click on the connection button brings it online. Server dashboard offers several information like the number of connected users, the port in use, the organization the server is connected to (when first configuring it it’s required to create and Organization and to assign it with the new server), and (optional) configured routes. The server can also be rebooted, shut down or deleted, while the central window of the panel provides information on logs or real-time bandwidth use.
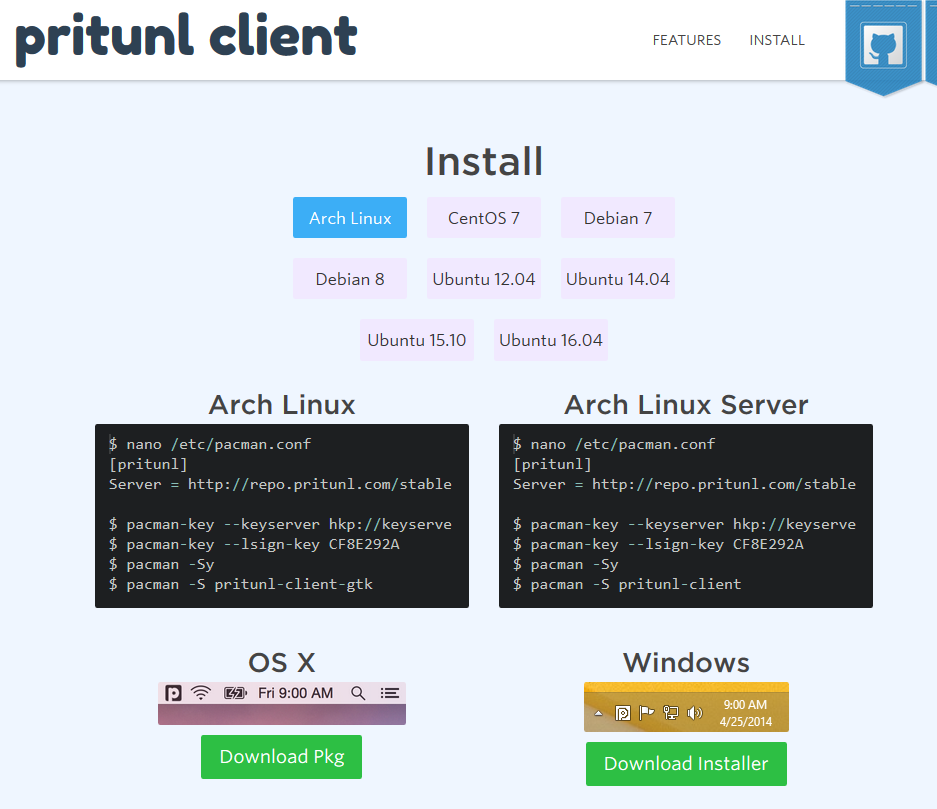
Once two users are created, as well as related organization and an associated (and started) server, we can go on with the installation of clients. As previously indicated, connection software is available for several platforms: in our case we have used two Windows machines (7 and 8.1 Professional) and a MacBook Pro with OS X 10.11. Pritunl’s client has gaudy colours and it’s quite intrusive, but not hard to use, with two buttons that clearly show the available options: inserting download url and uploading the configuration file downloaded from the Users panel. Both methods are equally efficient, yet the former is quicker and without intermediate steps: once the profile is loaded, the connection is ready to be established.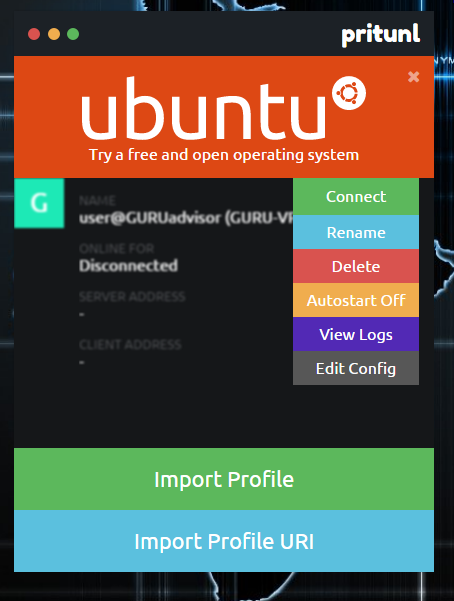
In our case we used a 6-cipher PIN as authentication method. Clicking the Connect button, a PIN is requested and, once inserted, the connection is established, showing the IP addresses of the server and the one assigned to the machine in use. As in the case of other OpenVPN software, on an operating system level a virtual network adapter is added, which will used by the client to route traffic on the VPN. This operation has to be repeated with all the clients that are to be connected to the VPN and, once connected, they will communicate on a secure and protected private network. Be careful when configuring server-side routes because, by default, a 0.0.0.0/0 rule is set, which indicates the routing of all Internet traffic of the client towards the VPN server, as it can be cause of browsing problems if it’s not adapted to the network in use. In a typical situation, indeed we do expect that only part of the traffic is routed through the VPN. The free version of Pritunl doesn’t allow NAT on the server, therefore it’s mandatory to configure, on the router itself, a dedicated rule to route traffic (incoming packets must be routed to the Pritunl server). Once properly configured the router, we can test the machines connected to the virtual network on the Internet by pinging them, to demonstrate a proper functioning state.
Pritunl proved to be an interesting solution to setup VPN architectures with an high degree of security and scalability: the price of the Enterprise license is probably significant for the smaller companies, yet reasonable considering all the features that are offered. The extreme ease of configuration, both server side and user side, is another point in favour of Pritunl, thanks to intuitive and well structured interfaces, and we’d also like to remark the good documentation with detailed tutorials that are explained in a clear and easy way.