DDoS attacks and botnets
Linux.MulDrop14 targets Raspberry-PI devices for cryptocurrencies mining
Dr.Web researchers discovered a malware, called Linux.MulDrop14, which targets Raspberry PI devices, the popular single board computer, adding them to a botnet that mines for cryptocurrencies.
In this case devices which still have default credentials and are reachable via SSH from the outside are vulnerable: the malware installs on the device, changes the access password and adds some packages, including libraries to start mining, ZMap to scan networks for vulnerable devices and sshpass to login on any found device.
Once infected, the only way to delete the malware is reinstalling the whole operating system. Naturally default passwords must be changed.
Here’s Magala, the aggressive advertising botnet
Kaspersky Labs announce the discovery of Magala, a new botnet used for aggressive advertising. Computers infected by the Magala Trojan Clicker perform fake ad visualizations, generating even $350 per computer per month. SMB in particular are hit by that as sometimes they rely on the wrong advertisers and pay for advertising that is void, as a matter of fact.
Magala, mostly active in Germany and the US, imitates the user behaviour on a web page incrementing the impression count of the site: once active, the malware contacts the C&C server to retrieve a list of site to work on.
Kaspersky Labs says that the average Cost Per Click (CPC) in such campaigns is $0.07, and the Cost Per Mille (CPM) is $2,2; a computer can easily generate £350 per month.
“Although this type of advertising fraud has long been known, the emergence of new botnets focusing on that area indicates that there is still a demand on half-legitimate promotion. Trying to cut their costs, small businesses go for that option, but spoil their ad efforts as a result. The success of Magala is yet another wake-up call for users to make the most of solid security solutions and keep all their software updated – in order to not fall victim to cybercriminals,” concludes Sergey Yunakovsky, security expert at Kaspersky Lab.
Study reveals that 15% of users doesn’t change the default credentials of IoT devices
A Positive Technology study (Positive technology is a security management and compliance provider) revealed some alarming data.
Worrisome data include the percentage of users that don’t change the default credentials of IoT devices - 15%- and the number of default passwords required to access to 10% of devices on the Net: 5.
These data help to define the size of a problem in the IoT field that is ever growing and whose security challenges will get harder and harder in the middle term: botnets like Mirai exploit brute-force attacks using a modest set of credentials (62 as stated in the study) as well as a modest engineering effort, yet the damage is amplified by the disregard of users.
As a consequence, strong awareness campaigns on the problem are required starting from professionals first, and this study provides numbers, data and interesting points of consideration.
Luckily producers are keeping up their products with a better intrinsic degree of security.
Ransomware
WannaCry is still active
More than a month after the original attacks, WannaCry is still active and keeps on infecting systems. No new infection campaign is going on, they’re just unpatched, thus vulnerable systems.
WannaCry infected 55 speed and red lights cameras in Australian state Victoria.
The incident happened during maintenance operations when an infected USB drive was connected to unpatched Windows devices.
A Honda manufacturing plant in Japan had to stop its production due to WannaCry, which probably was imported due to a single infected device that, after being installed, infected all systems on the network.
ID Ransomware now identifies more than 400 different ransomware
ID Ransomware, the online tool that identifies which malware encrypted a sample of data, can now identify more than 400 different kinds ransomware.
This tool, created by Michael Gillespie, is very easy to use: all you need to do is to upload either the ransom note, an encrypted file or the email addresses contained in the ransom note in order to identify which ransomware encrypted your data.
Moreover, if a decryption tool is available, the service will show you.
Decryption tools for XData, Jaff, EncrypTile, NemucodAES, Mole02 CryptoMix, BTCWare, Executioner, Petya and Mischa released
Here’s our monthly list of new decryption tools released this month.
Kaspersky Labs created tools for XData and Jaff, both decryptable with the updated Rakhni tool as they belong to the same malware family. Before using the tool, stop any ransomware process from the Task Bar: msdns.exe, mssql.exe, or mscom.exe for XData, SKM_C224e9930.exe for Jaff.
Emsisoft now offers a tool for Nemucod.
BleepingComputer offers tools for Striked, DCry and Mole02. This work is the result of a collaboration with Michael Gillespie, author of the aforementioned ID Ransomware service. Gillespie himself then stated that he can decrypt file encrypted with Executioner: contact him if needing some help.
Avast released a tool for Encryptile and updated tools for less recent ransomware like AES_NI, BTCWare, CrySiS, Crypt888 and XData.
Lastly, Malwarebytes released a tool for Petya and its variants: Red Petya, Green Petya, Mischa and GoldenEye.
Locky ransomware returns and targets Windows XP and Vista systems
Locky seemed to have definitely disappeared, instead is coming back as Talos researchers warn in an article.
Locky is now distributed via spam emails with the Necurs botnet and is harmless on systems from Windows 7 onwards with Data Execution Prevention (DEP), but can be effective on XP and Vista.
The new version was released after Kaspersky Labs created a decryption tool for Jaff, the “heir” ransomware created by the same developers of Locky.
However, probably due to the hurry of having it in circulation again, the authors made some mistakes, making it ineffective on some operating systems, yet some anti-debugging measures have been added, thus making it impossible to study in a test VM.
Locky is distributed as a zip attachment to emails.
Vulnerabilities
Foscam cameras are full of vulnerabilities
Foscam cameras (which are sold white label to other companies like Opticam) have several security issues, as F-Secure warns in a document.
In particular two models -Foscam C2 and Opticam i5 HD- were analysed, and very likely the same vulnerabilities are to be found in other models too. F-Secure stated that Foscam cameras are rebranded and sold by other 14 brands: Chacon, Thomson, 7links, Opticam, Netis, Turbox, Novodio, Ambientcam, Nexxt, Technaxx, Qcam, Ivue, Ebode and Sab.
The 18 newly found vulnerabilities permit to take control of the device and, in some cases, of the local network too; vulnerabilities include non secure and hard coded default credentials, remote code injection, insufficient file and folder permissions, an hidden Telnet feature and a firewall that discloses information of credentials. A detailed and complete list is available at this link.
Foscam has been informed of these vulnerabilities long ago but hasn’t released any firmware update yet.
Devil’s Ivy is a new vulnerability contained in popular gSOAP library
Senrio researchers discovered a vulnerability, called Devil’s Ivy, which is contained in gSOAP (Simple Object Access Protocol), a popular toolkit that enables direct communication between devices on the same network using it.
The vulnerability gets its name from a plant, the devil’s ivy, which is almost impossible to eradicate once it infests an area: similarly, this vulnerability propagates by means of code reuse, as it’s part of a very popular toolkit used by developers and companies like IBM, Microsoft, Adobe and Xerox.
Devil’s Ivy, which was discovered in a security camera fro Axis Communications, exploits a buffer overflow vulnerability that permits remote code execution, thus allowing an hacker to access video feed or to prevent an user from accessing a feed, which are very severe security concerns.
Senrio recommends not to connect to a network any devices with gSOAP, to protect IoT devices and apply patches as soon as they come out.
Genivia, the company that develops gSOAP, released a patch.
Systemd bug allows hackers to hack Linux systems via DNS packets
A bug in systemd -the system and services manager in Linux- allows hackers to crash or take control of Linux systems with bogus DNS packets.
The vulnerability, which goes by the catalog number of CVE-2017-9445, was discovered by Chris Coulson of Canonical: “Certain sizes passed to dns_packet_new can cause it to allocate a buffer that's too small. A malicious DNS server can exploit this by responding with a specially
crafted TCP payload to trick systemd-resolved in to allocating a buffer that's too small, and subsequently write arbitrary data beyond the end of it.”
Written data can crash systemd or write data in memory, then execute code on the system.
Canonical released updates for Ubuntu 16.10 and 17.04, Red Hat states that the vulnerability doesn’t hit systemd versions contained in RHEL 7 while Debian reassure users: systemd-resolved is not enabled by default.
SambaCry targets old Linux NAS systems
As we warned in last May issue, vulnerability CVE-2017-7494 -so called SambaCry as it resembles WannaCry because it leverages the SMB protocol too- has been used for an exploit.
TrendMicro researchers identified a malware, called SHELLBIND, that targets in particular Linux NAS appliances and some other IoT devices.
SHELLBIND is a backdoor trojan that creates a remote shell on infected devices; it modifies firewall rules opening port 61422 TCP to allow the hacker to connect to the device, thus gaining complete control of it.
Only Samba versions from 3.5.0 are vulnerable; Samba released patches for versions 4.6.4, 4.5.10 and 4.4.14, which are available at this address.
If you’re locked in and can’t update Samba, add this string to the global configuration of the smb.conf file:nt pipe support = no
Then restart smbd.
News from the vendors
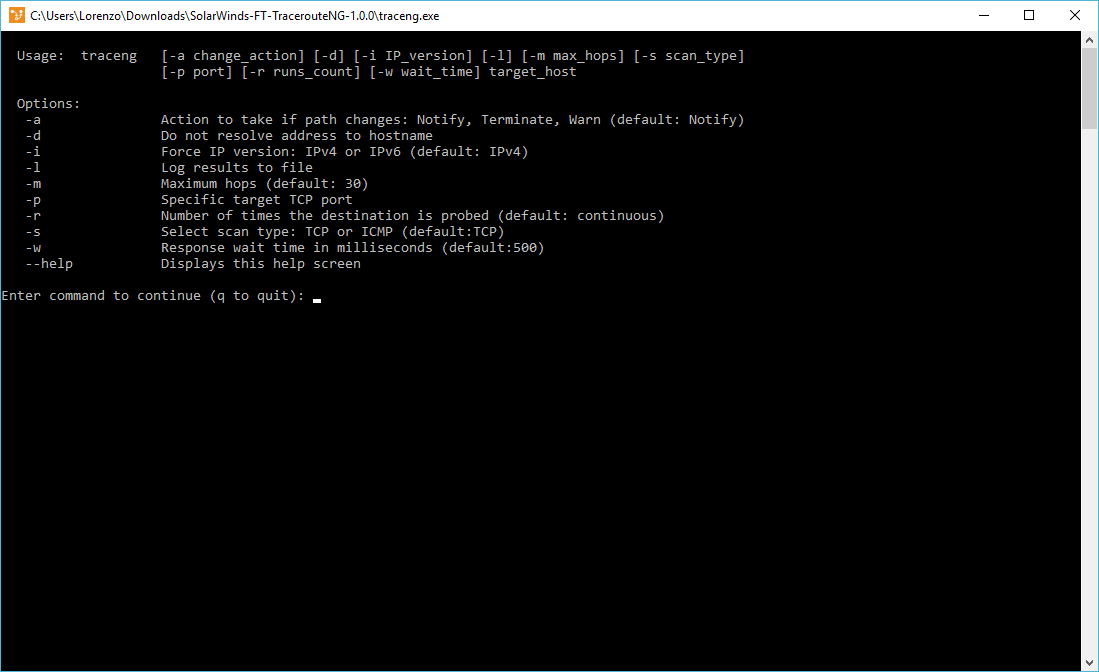
Eternal Blues warns if a host is vulnerable to ETERNAL BLUE
Elad Erez, security researcher, created an handy tool called Eternal Blues that permits to discover if an host is vulnerable to ETERNAL BLUE, the NSA exploit from NSA used by the WannaCry and NotPetya malware.
Despite being less advanced and complete than tools like NMap, Eternal Blues is easy and immediate to use; it also uses Google Analytics to collect data in an anonymous way. The tool is available at this address, and this page contains some interesting usage statistics: more than 8 million IP addresses check, of which 50% still have SMBv1 enabled, and 1 host out of 9 is vulnerable to ETERNAL BLUE.
How to behave if found vulnerable?
Apply Windows patch MS17-010, set update to automated, disable SMBv1 and check periodically the network’s security state with a dedicated scanning tool.
Apple releases security updates, also for the Broadpwn bug
Apple released several security updates, the most important is about the Broadpwn bug. This bug lets an hacker take control of an iOS device equipped with a particular Broadcom wifi chipset; the bug is fixed for watchOS, macOS and tvOS, in addition to iOS.
Other security updates are about tvOS, iTunes and iCloud for Windows, Safari, macOS, iOS and watchOS.
Android releases a patch for the Broadpwn bug
Android too released a bug for the Broadpwn bug which affects devices with Broadcom BCM43xx family wifi chipsets and are vulnerable to hacking attacks.
Further information about the bug are available at this address.
The patch is contained in the July monthly security update.
Avast acquires Piriform
Avast acquired Piriform, the security software house mostly known for CClear, a tool used by more than 130 million users, of which 15 are Android users.
Piriform also develops other tool for computer maintenance like Recuva (to retrieve deleted files), Speccy (collect system info) and Defraggler (disk defragmentation).
“The CCleaner brand fits very well to Avast, for various reasons. We both believe in high-quality free products. People won’t just use a product because it is free. It’s quite the opposite, if you are providing a free product, you need to convince people that your product is free, but not cheap. You need to provide a pretty damn good product so people will use it and recommend it to their family and friends. Like Avast, Piriform provides a fully functioning product for free, with some excellent premium features on top, like disk defragmenting, file recovery, and hardware inventory.
We will maintain the Piriform products separately from our current Avast optimization portfolio, and Piriform customers can rest assured they will continue to get the attention and service they are used to”, says Vince Steckler, Avast CEO.
Adobe released several patches for Flash Player
Adobe released 12 patches for Flash Player in the last week.
June security bulletins contained updates for Flash Player and other Adobe products like Shockwave Player, Captivate and Digital Editions.
Patches for Flash Players fix issues related to Remote Code Execution vulnerabilities.
July security bulletins contain updates for Adobe Connect and Flash Player. In this case too patches fix issues related to Remote Code Execution, which can lead an hacker to take control on the unpatched system, and to Information Disclosure and Memory Address Disclosure.
We suggest to update as soon as possible.
Microsoft’s July Patch Tuesday fixes 55 security problems
Patch Tuesday, the cumulative monthly update from Microsoft, has been released the second tuesday of the month. This month’s patches contain 55 security updates.
Products being updated are Internet Explorer, Microsoft Edge, Microsoft Windows, Microsoft Office e Microsoft Office Services and Web Apps, .NET Framework, Adobe Flash Player and Microsoft Exchange Server.
As Microsoft ceased last april to provide a complete bulletin on updates, you can use this PowerShell script by John Lambert (Microsoft employee) to obtain precise and detailed information about patches.
A complete and detailed list of updates is available at this address.
Google too won’t support StartCom SSL certificates
Google won’t support SSL certificates released by StartCom (and its mother-company WoSign) starting from the next version of Chrome -61-, expected in September.
The reason for that is the impossibility of the vendor to maintain the high standards required to CAs (Certificate Authorities).
In August 2016 Google was warned by the security team at GitHub that WoSign released a certificate to a GitHub domain to a user without authorization. The investigation led with Mozilla uncovered several other certificates released by WoSign without authorization.
Apple and Mozilla too don’t support certificates released by StartCom and WoSign.