Devices under control
Once decided to adopt a BYOD policy, it’s essential that the IT staff is prepared to handle such situation.
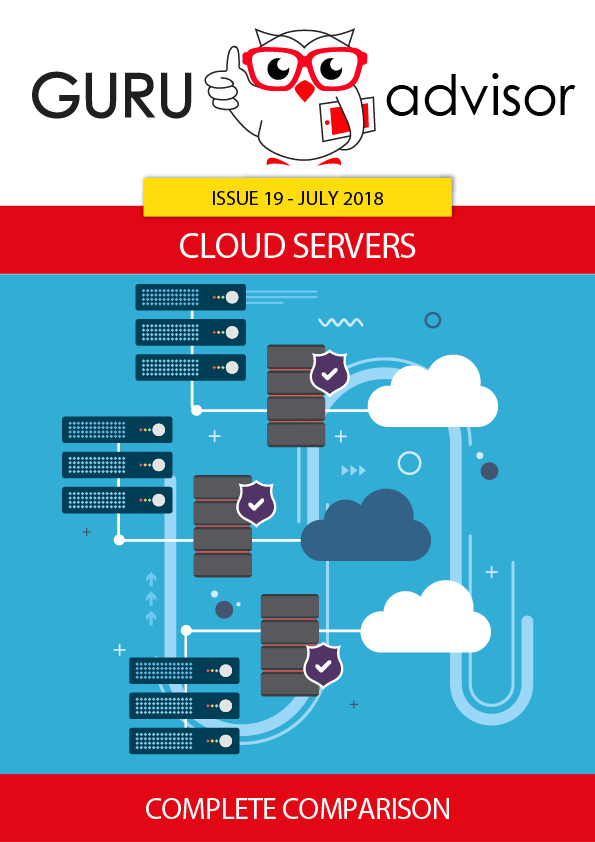
Manual management of each device is to be obviously excluded, the solution is clearly the use of dedicated software for an automatic and centralized control of the devices. Even if the notebook can  connect without any bandwidth problem, some things has to be inspected: the presence of an updated OS and an updated antivirus program, the presence of potentially dangerous files, the correct configuration of the remote connection and so forth. When one of those security conditions is lacking, it’s the system’s job to acknowledge of the problem and to temporarily isolate the device until properly restored.
connect without any bandwidth problem, some things has to be inspected: the presence of an updated OS and an updated antivirus program, the presence of potentially dangerous files, the correct configuration of the remote connection and so forth. When one of those security conditions is lacking, it’s the system’s job to acknowledge of the problem and to temporarily isolate the device until properly restored.
Untill a few years ago, a separation between the analysis of the mobile (smartphones and tables) and the notebooks world (be it PC or Mac) was necessary, but the quick evolution of the mobile Operative Systems practically puts them on the same level. Nowadays a notebook and a smartphone are capable of storing tens of GB of data, both platforms have problems linked to upgrade releases and the number of malicious software available is ever increasing. Who manages the machine compliance has to guarantee the access only to those who utilize hardware and software perfectly in order.